What Cisco Catalyst switch feature can be used to define ports as trusted for DHCP server connections?
A. DHCP snooping
B. port security
C. 802.1x
D. private VLANs
Explanation:
DHCP snooping is used to define ports as trusted for DHCP server connections. The purpose of DHCP snooping is to mitigate DHCP spoofing attacks. DHCP spoofing is an attack that can be used to force user traffic through an attacking device. This is accomplished by an attacker responding to DHCP queries from users. Eliminating the response from the correct DHCP server would make this more effective, but if the attacker’s response gets to the client first, the client will accept it.
The DHCP response from the attacker will include a different gateway or DNS server address. If they define a different gateway, the user traffic will be forced to travel through a device controlled by the attacker. This will allow the attacker to capture traffic and gain company information. If the attacker changes the DNS server in the response, they can use their own DNS server to force traffic to selected hosts to go to a device they control. Again, this would allow the attacker to capture traffic and gain information.
DHCP snooping can be used to determine what ports are able to send DHCP server packets, such as DHCPOFFER, DHCPACK, and DHCPNAK, from the company DHCP server. DHCP snooping can also cache the MAC address to IP address mapping for clients receiving DHCP addresses from a valid DHCP server.
The three required steps to implement DHCP snooping are:
1. Enable DHCP snooping globally with the ip dhcp snooping command:
switch(config)# ip dhcp snooping
2. Enable DHCP snooping for a VLAN with the vlan parameter:
switch(config)# ip dhcp snooping vlan vlan #
(for example, ip dhcp snooping 10 12 specifies snooping on VLANs 10 and 12)
3. Define an interface as a trusted DHCP port with the trust parameter:
switch(config-if)# ip dhcp snooping trust
When specifying trusted ports, access ports on edge switches should be configured as untrusted, with the exception of any ports that may have company DHCP severs connected. Only ports where DHCP traffic is expected should be trusted. Most certainly, ports in any area of the network where attacks have been detected should be configured as untrusted.
Some additional parameters that can be used with the ip dhcp snooping command are:
switch(config)# ip dhcp snooping verify mac-address – this command enables DHCP MAC address verification.
switch(config)# ip dhcp snooping information option allow-untrusted – this command enables untrusted ports to accept incoming DHCP packets with option 82 information. DHCP option 82 is used to identify the location of a DHCP relay agent operating on a subnet remote to the DHCP server.
When DHCP snooping is enabled, no other relay agent-related commands are available. The disabled commands include:
ip dhcp relay information check global configuration ip dhcp relay information policy global configuration
ip dhcp relay information trust-all global configuration ip dhcp relay information option global configuration
ip dhcp relay information trusted interface configuration
Private VLANs are a method of protecting or isolating different devices on the same port and VLAN. A VLAN can be divided into private VLANs, where some devices are able to access other devices and some are completely isolated from others. This was designed so service providers could keep customers on the same port isolated from each other, even if the customers had the same Layer 3 networks.
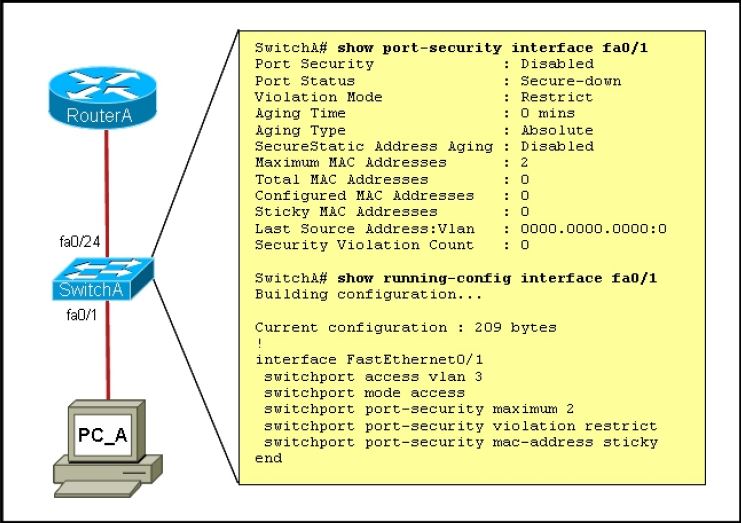
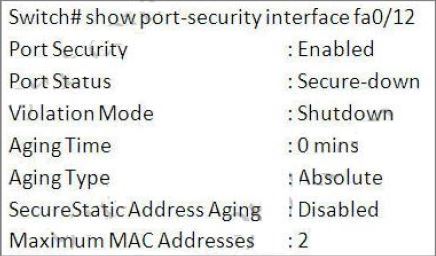
Port security is a method of only permitting specified MAC addresses access to a switch port. This can be used to define what computer or device can be connected to a port, but not to limit which ports can have DHCP servers connected to them.
802.1x is a method of determining authentication before permitting access to a switch port. This is useful in restricting who can connect to the switch, but it cannot control which ports are permitted to have a DHCP server attached to it.